With 1Password Business, you can use automated provisioning to centralize access management in your account. Depending on your setup, you’ll connect your identity provider using automated provisioning. If you deploy a SCIM bridge, also make sure to read best practices for the SCIM bridge.
1Password Business supports two types of integrations with identity providers, and each has its own benefits:
| Automated provisioning | Unlock with SSO | |
|---|---|---|
| Features | Automated user and group provisioning, role-based access control, and administrative workflows automation. | Team members can unlock 1Password with their identity provider credentials using the OpenID Connect (OIDC) protocol. |
| Methodology | Uses an API endpoint or SCIM bridge, which communicates with the 1Password servers using an encryption protocol called Secure Remote Password (SRP). | Uses a direct API integration with the 1Password servers. |
In this article, you’ll learn best practices for automated provisioning. If you want to allow your team to unlock 1Password with their identity provider credentials, learn about the best practices for using 1Password Unlock with SSO.
Plan your rollout
When you first set up automated provisioning, it won’t affect your account until you assign 1Password to users in your identity provider. Make sure you add a user or group who can test the integration. We don’t recommend adding your whole team right away. Gradually add groups of users to make sure the rollout goes smoothly.
Automated provisioning can help your team with:
- Group management: Groups in your identity provider can be imported to 1Password and group membership can be managed from your identity provider.
- Onboarding users: You can invite users to 1Password from your identity provider. New users are confirmed automatically after they sign up (see Provision users for how timing differs by integration).
- User management: When you change a user’s email address or display name in your identity provider, those changes will also be reflected in 1Password.
- Offboarding users: When you deprovision a user in your identity provider, their account will be suspended in 1Password.
After you set up automated provisioning, you’ll see a new group in your account called Provision Managers. It’s required for automated provisioning, so don’t delete it. Do not add any users to this group.
Add groups
Before you add a group to 1Password:
- Create one or more vaults for the group to store and share items in.
- If there are people in a group that you don’t want provisioned to 1Password (for example, directory service account identities), you must set up filters in your identity provider to exclude them.
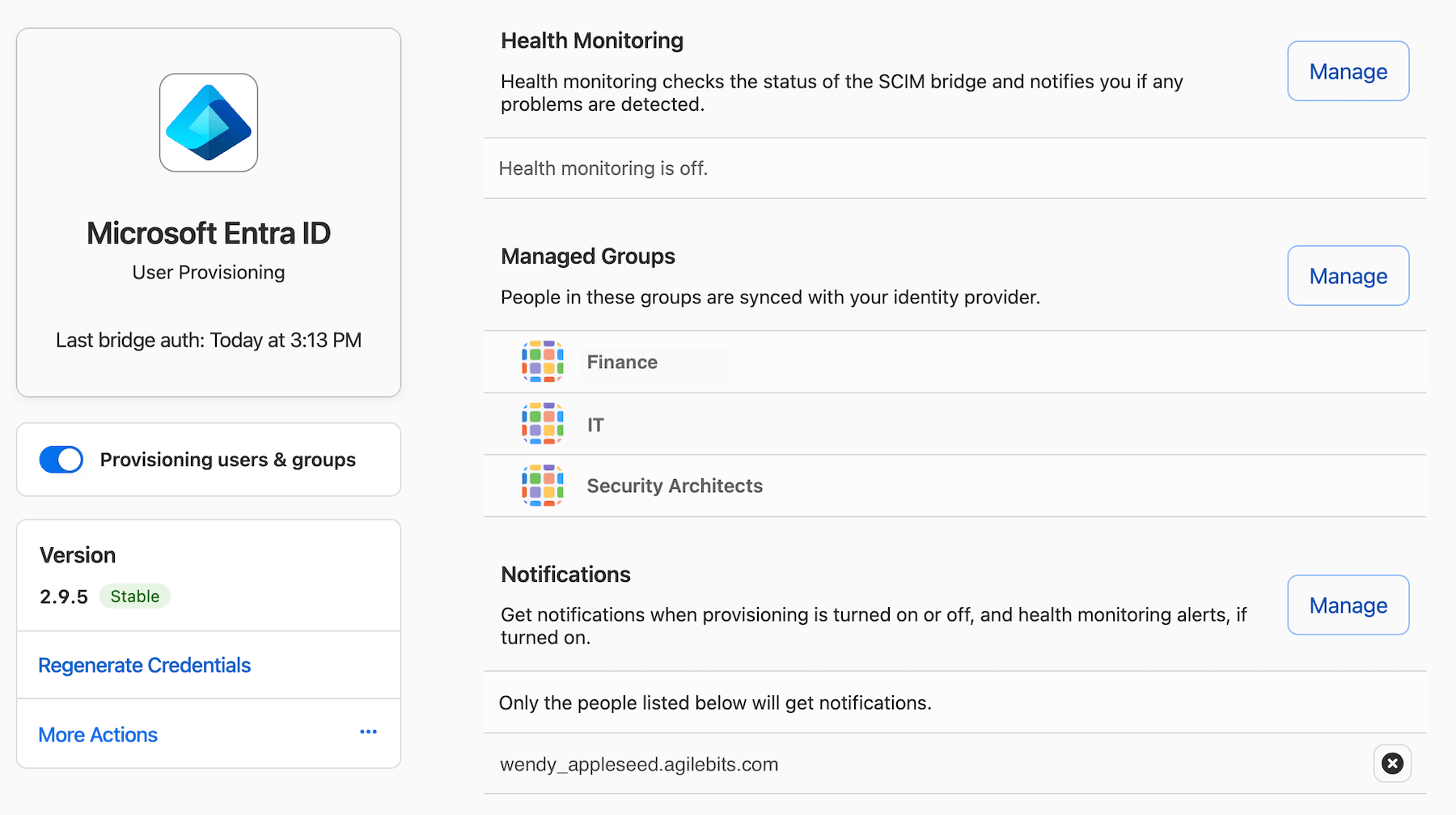
When you assign groups in your identity provider, the users in each group will be provisioned to 1Password. You can manage group permissions, create custom administrative roles, and grant vault access to groups from the Groups page of your account on 1Password.com. You can also view and update the list of provisioned groups in your account from the Managed Groups section of the Automated User Provisioning page.
We recommend that you follow the principle of least privilege and only grant the group, vault permissions, and access that each person needs for their role in the organization.
Important
Okta doesn’t automatically create groups in 1Password when you assign groups to an application. To use groups for role-based access control, turn on Okta’s Group Push feature to push directory groups into 1Password. Only users assigned to the application in Okta are included in the groups that appear in 1Password. Learn more about automated provisioning with Okta.
It can be helpful to create a group with all of your 1Password users, then provision the group in addition to your functional groups. The benefit is that users belong to at least one group, so moving them from one group to another for role-based access control won’t temporarily suspend their 1Password account.
1Password does not support nested groups or role assignments.
Provision users
You can invite users individually to test automated provisioning, or provision them with groups when you’re ready to start your rollout. With automated provisioning, users are confirmed automatically. There’s no need for an administrator to manually approve them afterward.
When you assign a user or group to 1Password in your identity provider:
- They’ll receive an invite email.
- They’ll follow the steps to sign up.
- Your integration will confirm the new user automatically. With automated provisioning, users are confirmed when they accept the invitation. If you use a SCIM bridge, the bridge typically confirms the user within five minutes.
- They’ll get another email letting them know they can start using their account.
If a user with the same email address already exists in 1Password, they won’t be invited to the account or receive any notification about the invitation. Only new users who don’t have an account with their email address will receive an invite email.
Manage users
Manage existing team members
If you already have team members in your 1Password account before you start automated provisioning, you’ll need to assign them to 1Password in your identity provider. Assigned directory users will be matched based on the team member’s email address in 1Password, and they can then be managed by your identity provider.
Edit user details
When you edit user details in your directory, such as display names or email addresses, the changes will be synchronized to 1Password.
Learn how to change a team member’s email address.
Deprovision team members
There are a few ways to deprovision a managed team member:
- Delete the user from your identity provider.
- Deactivate their user profile in your identity provider.
- Remove the user from all groups in your directory that are assigned to 1Password (or remove the group assignment), and remove any explicit user assignments.
After a user is taken out of the provisioning scope, their 1Password account will be suspended. We recommend you keep their account suspended for a set amount of time, such as a month, before you delete it, in case you need to recover their data. You can only delete a user’s 1Password account after they’ve been deprovisioned. Learn more about how to offboard a team member.
Learn more
- Set up 1Password automated provisioning
- Best practices for securing your 1Password Business account
- Best practices for 1Password SCIM Bridge
Was this article helpful?
Glad to hear it! If you have anything you'd like to add, feel free to contact us.
Sorry to hear that. Please contact us if you'd like to provide more details.